Review:
Night Watch, by Terry Pratchett
| Series: |
Discworld #29 |
| Publisher: |
Harper |
| Copyright: |
November 2002 |
| Printing: |
August 2014 |
| ISBN: |
0-06-230740-1 |
| Format: |
Mass market |
| Pages: |
451 |
Night Watch is the 29th Discworld novel and the sixth Watch novel.
I would really like to tell people they could start here if they wanted
to, for reasons that I will get into in a moment, but I think I would be
doing you a disservice. The emotional heft added by having read the
previous Watch novels and followed Vimes's character evolution is
significant.
It's the 25th of May. Vimes is about to become a father. He and several
of the other members of the Watch are wearing sprigs of lilac for reasons
that Sergeant Colon is quite vehemently uninterested in explaining. A
serial killer named Carcer the Watch has been after for weeks has just
murdered an off-duty sergeant. It's a tense and awkward sort of day and
Vimes is feeling weird and wistful, remembering the days when he was a
copper and not a manager who has to dress up in ceremonial armor and meet
with committees.
That may be part of why, when the message comes over the clacks that the
Watch have Carcer cornered on the roof of the New Hall of the Unseen
University, Vimes responds in person. He's grappling with Carcer on the
roof of the University Library in the middle of a magical storm when
lightning strikes. When he wakes up, he's in the past, shortly after he
joined the Watch and shortly before the events of the 25th of May that the
older Watch members so vividly remember and don't talk about.
I have been saying recently in Discworld reviews that it felt like
Pratchett was on the verge of a breakout book that's head and shoulders
above Discworld prior to that point. This is it. This is that book.
The setup here is masterful: the sprigs of lilac that slowly tell the
reader something is going on, the refusal of any of the older Watch
members to talk about it, the scene in the graveyard to establish the
stakes, the disconcerting fact that Vetinari is wearing a sprig of lilac
as well, and the feeling of building tension that matches the growing
electrical storm. And Pratchett never gives into the temptation to
explain everything and tip his hand prematurely. We know the 25th is
coming and something is going to happen, and the reader can put together
hints from Vimes's thoughts, but Pratchett lets us guess and sometimes be
right and sometimes be wrong. Vimes is trying to change history, which
adds another layer of uncertainty and enjoyment as the reader tries to
piece together both the true history and the changes. This is a masterful
job at a "what if?" story.
And, beneath that, the commentary on policing and government and ethics is
astonishingly good. In a review of an earlier Watch novel, I
compared Pratchett to Dickens in the way that
he focuses on a sort of common-sense morality rather than political
theory. That is true here too, but oh that moral analysis is sharp enough
to slide into you like a knife. This is not the Vimes that we first met
in
Guards! Guards!. He has has turned
his cynical stubbornness into a working theory of policing, and it's
subtle and complicated and full of nuance that he only barely knows how to
explain. But he knows how to show it to people.
Keep the peace. That was the thing. People often failed to
understand what that meant. You'd go to some life-threatening
disturbance like a couple of neighbors scrapping in the street over
who owned the hedge between their properties, and they'd both be
bursting with aggrieved self-righteousness, both yelling, their wives
would either be having a private scrap on the side or would have
adjourned to a kitchen for a shared pot of tea and a chat, and they
all expected you to sort it out.
And they could never understand that it wasn't your job. Sorting it
out was a job for a good surveyor and a couple of lawyers, maybe.
Your job was to quell the impulse to bang their stupid fat heads
together, to ignore the affronted speeches of dodgy
self-justification, to get them to stop shouting and to get them off
the street. Once that had been achieved, your job was over. You
weren't some walking god, dispensing finely tuned natural justice.
Your job was simply to bring back peace.
When Vimes is thrown back in time, he has to pick up the role of his own
mentor, the person who taught him what policing should be like. His
younger self is right there, watching everything he does, and he's
desperately afraid he'll screw it up and set a worse example. Make
history worse when he's trying to make it better. It's a beautifully
well-done bit of tension that uses time travel as the hook to show both
how difficult mentorship is and also how irritating one's earlier naive
self would be.
He wondered if it was at all possible to give this idiot some lessons
in basic politics. That was always the dream, wasn't it? "I wish I'd
known then what I know now"? But when you got older you found out
that you now wasn't you then. You then was a twerp.
You then was what you had to be to start out on the rocky road of
becoming you now, and one of the rocky patches on that road was being
a twerp.
The backdrop of this story, as advertised by the map at the front of the
book, is a revolution of sorts. And the revolution does matter, but not
in the obvious way. It creates space and circumstance for some other
things to happen that are all about the abuse of policing as a tool of
politics rather than Vimes's principle of keeping the peace. I mentioned
when reviewing
Men at Arms that it was
an awkward book to read in the United States in 2020. This book tackles
the ethics of policing head-on, in exactly the way that book didn't.
It's also a marvelous bit of competence porn. Somehow over the years,
Vimes has become extremely good at what he does, and not just in the
obvious cop-walking-a-beat sort of ways. He's become a leader. It's not
something he thinks about, even when thrown back in time, but it's
something Pratchett can show the reader directly, and have the other
characters in the book comment on.
There is so much more that I'd like to say, but so much would be spoilers,
and I think
Night Watch is more effective when you have the
suspense of slowly puzzling out what's going to happen. Pratchett's
pacing is exquisite. It's also one of the rare Discworld novels where
Pratchett fully commits to a point of view and lets Vimes tell the story.
There are a few interludes with other people, but the only other
significant protagonist is, quite fittingly, Vetinari. I won't say
anything more about that except to note that the relationship between
Vimes and Vetinari is one of the best bits of fascinating subtlety in all
of Discworld.
I think it's also telling that nothing about
Night Watch reads as
parody. Sure, there is a nod to
Back to the Future in the
lightning storm, and it's impossible to write a book about police and
street revolutions without making the reader think about
Les
Miserables, but nothing about this plot matches either of those stories.
This is Pratchett telling his own story in his own world,
unapologetically, and without trying to wedge it into parody shape, and it
is so much the better book for it.
The one quibble I have with the book is that the bits with the Time Monks
don't really work. Lu-Tze is annoying and flippant given the emotional
stakes of this story, the interludes with him are frustrating and out of
step with the rest of the book, and the time travel hand-waving doesn't add
much. I see structurally why Pratchett put this in: it gives Vimes (and
the reader) a time frame and a deadline, it establishes some of the ground
rules and stakes, and it provides a couple of important opportunities for
exposition so that the reader doesn't get lost. But it's not good story.
The rest of the book is so amazingly good, though, that it doesn't matter
(and the framing stories for "what if?" explorations almost never make
much sense).
The other thing I have a bit of a quibble with is outside the book.
Night Watch, as you may have guessed by now, is the origin of the
May 25th Pratchett memes that you will be familiar with if you've spent
much time around SFF fandom. But this book is dramatically different from
what I was expecting based on the memes. You will, for example see a lot
of people posting "Truth, Justice, Freedom, Reasonably Priced Love, And a
Hard-Boiled Egg!", and before reading the book it sounds like a
Pratchett-style humorous revolutionary slogan. And I guess it is, sort
of, but, well... I have to quote the scene:
"You'd like Freedom, Truth, and Justice, wouldn't you, Comrade
Sergeant?" said Reg encouragingly.
"I'd like a hard-boiled egg," said Vimes, shaking the match out.
There was some nervous laughter, but Reg looked offended.
"In the circumstances, Sergeant, I think we should set our sights a
little higher "
"Well, yes, we could," said Vimes, coming down the steps. He glanced
at the sheets of papers in front of Reg. The man cared. He really
did. And he was serious. He really was. "But...well, Reg, tomorrow
the sun will come up again, and I'm pretty sure that whatever happens
we won't have found Freedom, and there won't be a whole lot of
Justice, and I'm damn sure we won't have found Truth. But it's just
possible that I might get a hard-boiled egg."
I think I'm feeling defensive of the heart of this book because it's such
an emotional gut punch and says such complicated and nuanced things about
politics and ethics (and such deeply cynical things about revolution).
But I think if I were to try to represent this story in a meme, it would
be the "angels rise up" song, with all the layers of meaning that it gains
in this story. I'm still at the point where the lilac sprigs remind me of
Sergeant Colon becoming quietly furious at the overstep of someone who
wasn't there.
There's one other thing I want to say about that scene: I'm not naturally
on Vimes's side of this argument. I think it's important to note that
Vimes's attitude throughout this book is profoundly, deeply conservative.
The hard-boiled egg captures that perfectly: it's a bit of physical
comfort, something you can buy or make, something that's part of the
day-to-day wheels of the city that Vimes talks about elsewhere in
Night Watch. It's a rejection of revolution, something that Vimes
does elsewhere far more explicitly.
Vimes is a cop. He is in some profound sense a defender of the status
quo. He doesn't believe things are going to fundamentally change, and
it's not clear he would want them to if they did.
And yet. And yet, this is where Pratchett's Dickensian morality comes
out. Vimes is a conservative at heart. He's grumpy and cynical and jaded
and he doesn't like change. But if you put him in a situation where
people are being hurt, he will break every rule and twist every principle
to stop it.
He wanted to go home. He wanted it so much that he trembled at the
thought. But if the price of that was selling good men to the night,
if the price was filling those graves, if the price was not fighting
with every trick he knew... then it was too high.
It wasn't a decision that he was making, he knew. It was happening
far below the areas of the brain that made decisions. It was
something built in. There was no universe, anywhere, where a Sam
Vimes would give in on this, because if he did then he wouldn't be Sam
Vimes any more.
This is truly exceptional stuff. It is the best Discworld novel I have
read, by far. I feel like this was the Watch novel that Pratchett was
always trying to write, and he had to write five other novels first to
figure out how to write it. And maybe to prepare Discworld readers to
read it.
There are a lot of Discworld novels that are great on their own merits,
but also it is 100% worth reading all the Watch novels just so that you
can read this book.
Followed in publication order by
The Wee Free Men and later,
thematically, by
Thud!.
Rating: 10 out of 10

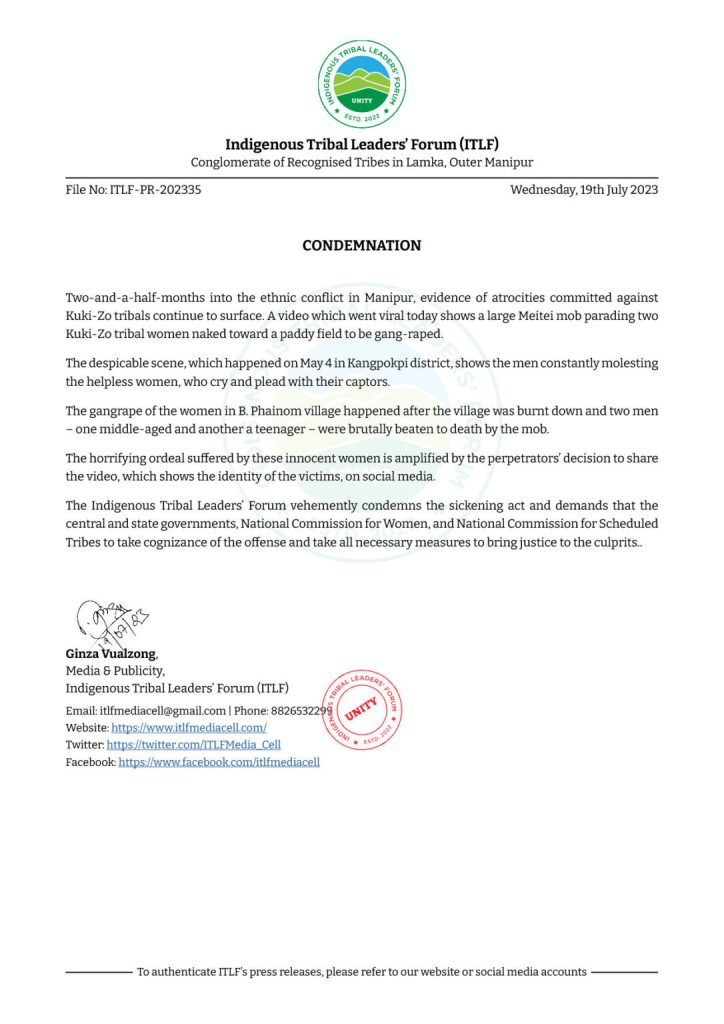
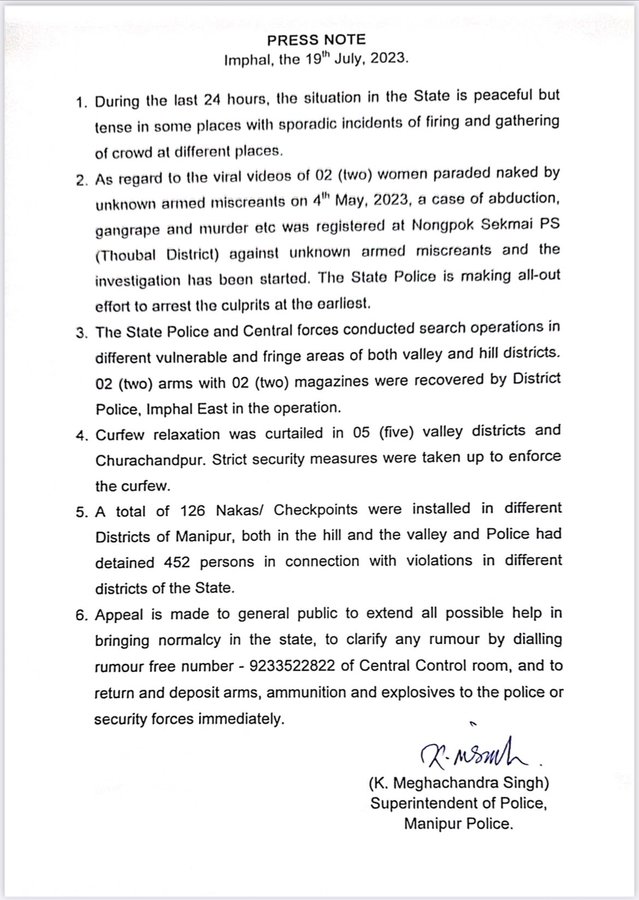
 A real sad state of affairs
A real sad state of affairs  Update: There is conditional reopening whatever that means
Update: There is conditional reopening whatever that means  When I saw the videos, the first thing is I felt was being powerless, powerless to do anything about it. The second was if I do not write about it, amplify it and don t let others know about it then what s the use of being able to blog
When I saw the videos, the first thing is I felt was being powerless, powerless to do anything about it. The second was if I do not write about it, amplify it and don t let others know about it then what s the use of being able to blog 
 While I felt a bit foolish, I felt it would be nice to binge on some webseries. Little I was to know that both Northshore and Alaska Daily would have stories similar to what is happening here
While I felt a bit foolish, I felt it would be nice to binge on some webseries. Little I was to know that both Northshore and Alaska Daily would have stories similar to what is happening here  While the story in Alaska Daily is fictional it resembles very closely to a real newspaper called Anchorage Daily news. Even there the Intuit women , one of the marginalized communities in Alaska. The only difference I can see between GOI and the Alaskan Government is that the Alaskan Government was much subtle in doing the same things. There are some differences though. First, the State is and was responsive to the local press and apart from one close call to one of its reporters, most reporters do not have to think about their own life in peril. Here, the press cannot look after either their livelihood or their life. It was a juvenile kid who actually shot the video, uploaded and made it viral. One needs to just remember the case details of Siddique Kappan. Just for sharing the news and the video he was arrested. Bail was denied to him time and time again citing that the Police were investigating . Only after 2 years and 3 months he got bail and that too because none of the charges that the Police had they were able to show any prima facie evidence.
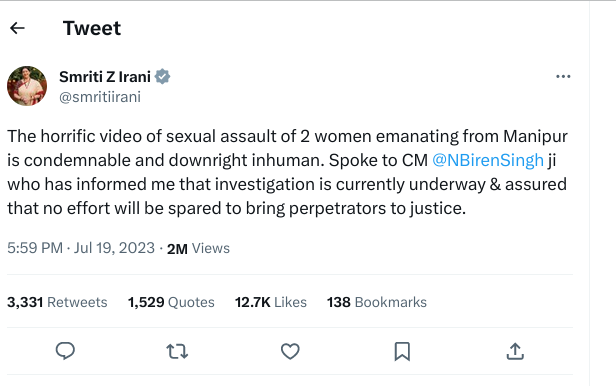
One of the better interviews though was of Vrinda Grover. For those who don t know her, her Wikipedia page does tell a bit about her although it is woefully incomplete. For example, most recently she had relentlessly pursued the unconstitutional Internet Shutdown that happened in Kashmir for 5 months. Just like in Manipur, the shutdown was there to bury crimes either committed or being facilitated by the State. For the issues of livelihood, one can take the cases of Bipin Yadav and Rashid Hussain. Both were fired by their employer Dainik Bhaskar because they questioned the BJP MP Smriti Irani what she has done for the state. The problems for Dainik Bhaskar or for any other mainstream media is most of them rely on Government advertisements. Private investment in India has fallen to record lows mostly due to the policies made by the Centre. If any entity or sector grows a bit then either Adani or Ambani will one way or the other take it. So, for most first and second generation entrepreneurs it doesn t make sense to grow and then finally sell it to one of these corporates at a loss
While the story in Alaska Daily is fictional it resembles very closely to a real newspaper called Anchorage Daily news. Even there the Intuit women , one of the marginalized communities in Alaska. The only difference I can see between GOI and the Alaskan Government is that the Alaskan Government was much subtle in doing the same things. There are some differences though. First, the State is and was responsive to the local press and apart from one close call to one of its reporters, most reporters do not have to think about their own life in peril. Here, the press cannot look after either their livelihood or their life. It was a juvenile kid who actually shot the video, uploaded and made it viral. One needs to just remember the case details of Siddique Kappan. Just for sharing the news and the video he was arrested. Bail was denied to him time and time again citing that the Police were investigating . Only after 2 years and 3 months he got bail and that too because none of the charges that the Police had they were able to show any prima facie evidence.
One of the better interviews though was of Vrinda Grover. For those who don t know her, her Wikipedia page does tell a bit about her although it is woefully incomplete. For example, most recently she had relentlessly pursued the unconstitutional Internet Shutdown that happened in Kashmir for 5 months. Just like in Manipur, the shutdown was there to bury crimes either committed or being facilitated by the State. For the issues of livelihood, one can take the cases of Bipin Yadav and Rashid Hussain. Both were fired by their employer Dainik Bhaskar because they questioned the BJP MP Smriti Irani what she has done for the state. The problems for Dainik Bhaskar or for any other mainstream media is most of them rely on Government advertisements. Private investment in India has fallen to record lows mostly due to the policies made by the Centre. If any entity or sector grows a bit then either Adani or Ambani will one way or the other take it. So, for most first and second generation entrepreneurs it doesn t make sense to grow and then finally sell it to one of these corporates at a loss  GOI on Adani, Ambani side of any deal. The MSME sector that is and used to be the second highest employer hasn t been able to recover from the shocks of demonetization, GST and then the pandemic. Each resulting in more and more closures and shutdowns. Most of the joblessness has gone up tremendously in North India which the Government tries to deny.
The most interesting points in all those above examples is within a month or less, whatever the media reports gets scrubbed. Even the firing of the journos that was covered by some of the mainstream media isn t there anymore. I have to use secondary sources instead of primary sources. One can think of the chilling effects on reportage due to the above. The sad fact is even with all the money in the world the PM is unable to come to the Parliament to face questions.
GOI on Adani, Ambani side of any deal. The MSME sector that is and used to be the second highest employer hasn t been able to recover from the shocks of demonetization, GST and then the pandemic. Each resulting in more and more closures and shutdowns. Most of the joblessness has gone up tremendously in North India which the Government tries to deny.
The most interesting points in all those above examples is within a month or less, whatever the media reports gets scrubbed. Even the firing of the journos that was covered by some of the mainstream media isn t there anymore. I have to use secondary sources instead of primary sources. One can think of the chilling effects on reportage due to the above. The sad fact is even with all the money in the world the PM is unable to come to the Parliament to face questions.

 Even the media landscape has been altered substantially within the last few years. Both Adani and Ambani have distributed the media pie between themselves. One of the last bastions of the free press, NDTV was bought by Adani in a hostile takeover. Both Ambani and Adani are close to this Goverment. In fact, there is no sector in which one or the other is not present. Media houses like Newsclick, The Wire etc. that are a fraction of mainstream press are where most of the youth have been going to get their news as they are not partisan. Although even there, GOI has time and again interfered. The Wire has had too many 504 Gateway timeouts in the recent months and they had been forced to move most of their journalism from online to video, rather Youtube in order to escape both the censoring and the timeouts as shared above. In such a hostile environment, how both the organizations are somehow able to survive is a miracle. Most local reportage is also going to YouTube as that s the best way for them to not get into Govt. censors. Not an ideal situation, but that s the way it is.
The difference between Indian and Israeli media can be seen through this
Even the media landscape has been altered substantially within the last few years. Both Adani and Ambani have distributed the media pie between themselves. One of the last bastions of the free press, NDTV was bought by Adani in a hostile takeover. Both Ambani and Adani are close to this Goverment. In fact, there is no sector in which one or the other is not present. Media houses like Newsclick, The Wire etc. that are a fraction of mainstream press are where most of the youth have been going to get their news as they are not partisan. Although even there, GOI has time and again interfered. The Wire has had too many 504 Gateway timeouts in the recent months and they had been forced to move most of their journalism from online to video, rather Youtube in order to escape both the censoring and the timeouts as shared above. In such a hostile environment, how both the organizations are somehow able to survive is a miracle. Most local reportage is also going to YouTube as that s the best way for them to not get into Govt. censors. Not an ideal situation, but that s the way it is.
The difference between Indian and Israeli media can be seen through this


 While I felt a bit foolish, I felt it would be nice to binge on some webseries. Little I was to know that both Northshore and Alaska Daily would have stories similar to what is happening here
While I felt a bit foolish, I felt it would be nice to binge on some webseries. Little I was to know that both Northshore and Alaska Daily would have stories similar to what is happening here  While the story in Alaska Daily is fictional it resembles very closely to a real newspaper called Anchorage Daily news. Even there the Intuit women , one of the marginalized communities in Alaska. The only difference I can see between GOI and the Alaskan Government is that the Alaskan Government was much subtle in doing the same things. There are some differences though. First, the State is and was responsive to the local press and apart from one close call to one of its reporters, most reporters do not have to think about their own life in peril. Here, the press cannot look after either their livelihood or their life. It was a juvenile kid who actually shot the video, uploaded and made it viral. One needs to just remember the case details of Siddique Kappan. Just for sharing the news and the video he was arrested. Bail was denied to him time and time again citing that the Police were investigating . Only after 2 years and 3 months he got bail and that too because none of the charges that the Police had they were able to show any prima facie evidence.
One of the better interviews though was of Vrinda Grover. For those who don t know her, her Wikipedia page does tell a bit about her although it is woefully incomplete. For example, most recently she had relentlessly pursued the unconstitutional Internet Shutdown that happened in Kashmir for 5 months. Just like in Manipur, the shutdown was there to bury crimes either committed or being facilitated by the State. For the issues of livelihood, one can take the cases of Bipin Yadav and Rashid Hussain. Both were fired by their employer Dainik Bhaskar because they questioned the BJP MP Smriti Irani what she has done for the state. The problems for Dainik Bhaskar or for any other mainstream media is most of them rely on Government advertisements. Private investment in India has fallen to record lows mostly due to the policies made by the Centre. If any entity or sector grows a bit then either Adani or Ambani will one way or the other take it. So, for most first and second generation entrepreneurs it doesn t make sense to grow and then finally sell it to one of these corporates at a loss
While the story in Alaska Daily is fictional it resembles very closely to a real newspaper called Anchorage Daily news. Even there the Intuit women , one of the marginalized communities in Alaska. The only difference I can see between GOI and the Alaskan Government is that the Alaskan Government was much subtle in doing the same things. There are some differences though. First, the State is and was responsive to the local press and apart from one close call to one of its reporters, most reporters do not have to think about their own life in peril. Here, the press cannot look after either their livelihood or their life. It was a juvenile kid who actually shot the video, uploaded and made it viral. One needs to just remember the case details of Siddique Kappan. Just for sharing the news and the video he was arrested. Bail was denied to him time and time again citing that the Police were investigating . Only after 2 years and 3 months he got bail and that too because none of the charges that the Police had they were able to show any prima facie evidence.
One of the better interviews though was of Vrinda Grover. For those who don t know her, her Wikipedia page does tell a bit about her although it is woefully incomplete. For example, most recently she had relentlessly pursued the unconstitutional Internet Shutdown that happened in Kashmir for 5 months. Just like in Manipur, the shutdown was there to bury crimes either committed or being facilitated by the State. For the issues of livelihood, one can take the cases of Bipin Yadav and Rashid Hussain. Both were fired by their employer Dainik Bhaskar because they questioned the BJP MP Smriti Irani what she has done for the state. The problems for Dainik Bhaskar or for any other mainstream media is most of them rely on Government advertisements. Private investment in India has fallen to record lows mostly due to the policies made by the Centre. If any entity or sector grows a bit then either Adani or Ambani will one way or the other take it. So, for most first and second generation entrepreneurs it doesn t make sense to grow and then finally sell it to one of these corporates at a loss  GOI on Adani, Ambani side of any deal. The MSME sector that is and used to be the second highest employer hasn t been able to recover from the shocks of demonetization, GST and then the pandemic. Each resulting in more and more closures and shutdowns. Most of the joblessness has gone up tremendously in North India which the Government tries to deny.
The most interesting points in all those above examples is within a month or less, whatever the media reports gets scrubbed. Even the firing of the journos that was covered by some of the mainstream media isn t there anymore. I have to use secondary sources instead of primary sources. One can think of the chilling effects on reportage due to the above. The sad fact is even with all the money in the world the PM is unable to come to the Parliament to face questions.
GOI on Adani, Ambani side of any deal. The MSME sector that is and used to be the second highest employer hasn t been able to recover from the shocks of demonetization, GST and then the pandemic. Each resulting in more and more closures and shutdowns. Most of the joblessness has gone up tremendously in North India which the Government tries to deny.
The most interesting points in all those above examples is within a month or less, whatever the media reports gets scrubbed. Even the firing of the journos that was covered by some of the mainstream media isn t there anymore. I have to use secondary sources instead of primary sources. One can think of the chilling effects on reportage due to the above. The sad fact is even with all the money in the world the PM is unable to come to the Parliament to face questions.

 Even the media landscape has been altered substantially within the last few years. Both Adani and Ambani have distributed the media pie between themselves. One of the last bastions of the free press, NDTV was bought by Adani in a hostile takeover. Both Ambani and Adani are close to this Goverment. In fact, there is no sector in which one or the other is not present. Media houses like Newsclick, The Wire etc. that are a fraction of mainstream press are where most of the youth have been going to get their news as they are not partisan. Although even there, GOI has time and again interfered. The Wire has had too many 504 Gateway timeouts in the recent months and they had been forced to move most of their journalism from online to video, rather Youtube in order to escape both the censoring and the timeouts as shared above. In such a hostile environment, how both the organizations are somehow able to survive is a miracle. Most local reportage is also going to YouTube as that s the best way for them to not get into Govt. censors. Not an ideal situation, but that s the way it is.
The difference between Indian and Israeli media can be seen through this
Even the media landscape has been altered substantially within the last few years. Both Adani and Ambani have distributed the media pie between themselves. One of the last bastions of the free press, NDTV was bought by Adani in a hostile takeover. Both Ambani and Adani are close to this Goverment. In fact, there is no sector in which one or the other is not present. Media houses like Newsclick, The Wire etc. that are a fraction of mainstream press are where most of the youth have been going to get their news as they are not partisan. Although even there, GOI has time and again interfered. The Wire has had too many 504 Gateway timeouts in the recent months and they had been forced to move most of their journalism from online to video, rather Youtube in order to escape both the censoring and the timeouts as shared above. In such a hostile environment, how both the organizations are somehow able to survive is a miracle. Most local reportage is also going to YouTube as that s the best way for them to not get into Govt. censors. Not an ideal situation, but that s the way it is.
The difference between Indian and Israeli media can be seen through this
















 The Rcpp Core Team is delighted to announce that the newest release
1.0.11 of the
The Rcpp Core Team is delighted to announce that the newest release
1.0.11 of the 










 It s been a very long time I haven t blogged about e-voting, although
some might remember it s been a topic I have long worked with;
particularly, it was the topic of
It s been a very long time I haven t blogged about e-voting, although
some might remember it s been a topic I have long worked with;
particularly, it was the topic of 
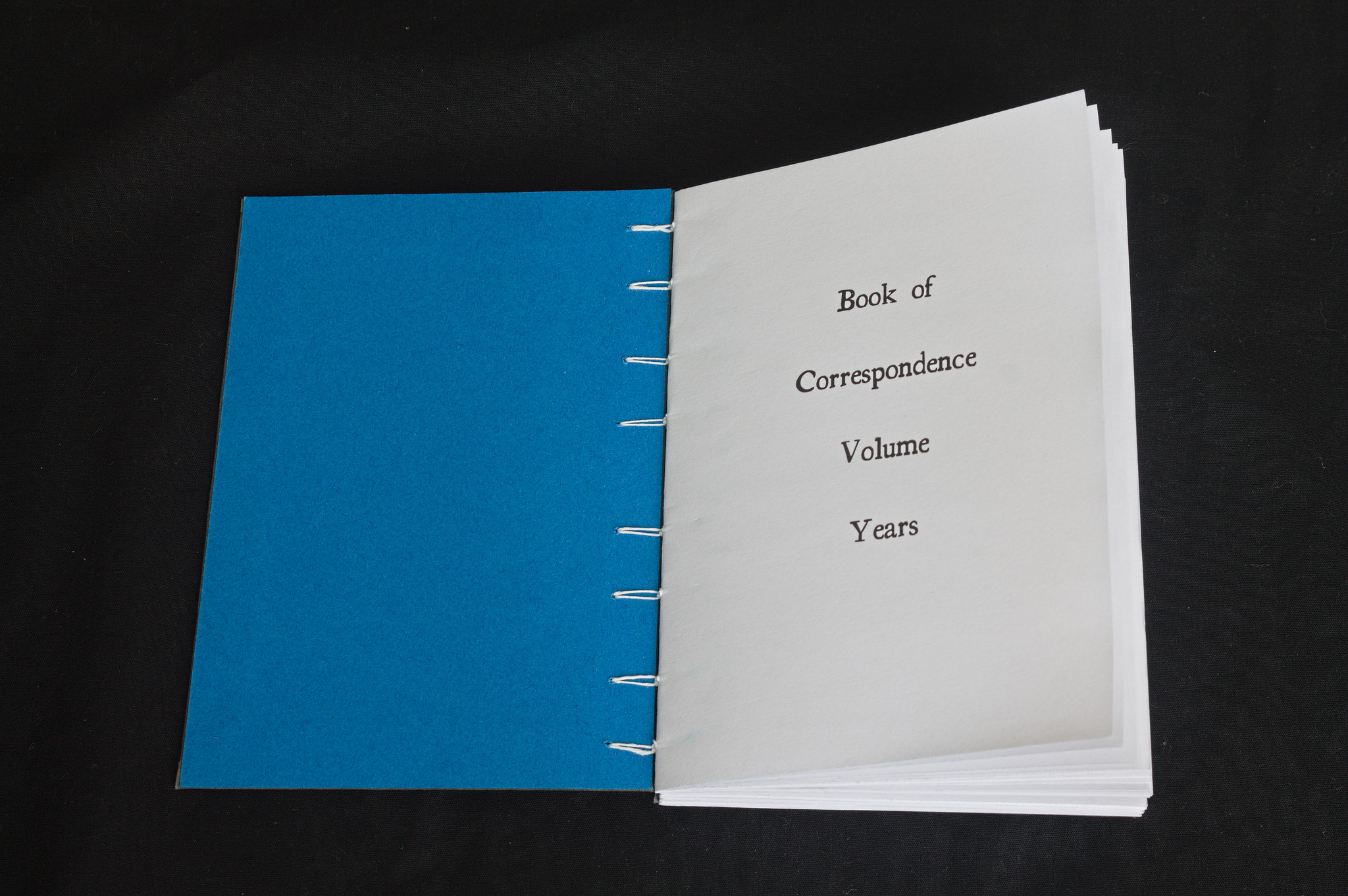 I write letters. The kind that are written on paper with a dip pen
I write letters. The kind that are written on paper with a dip pen 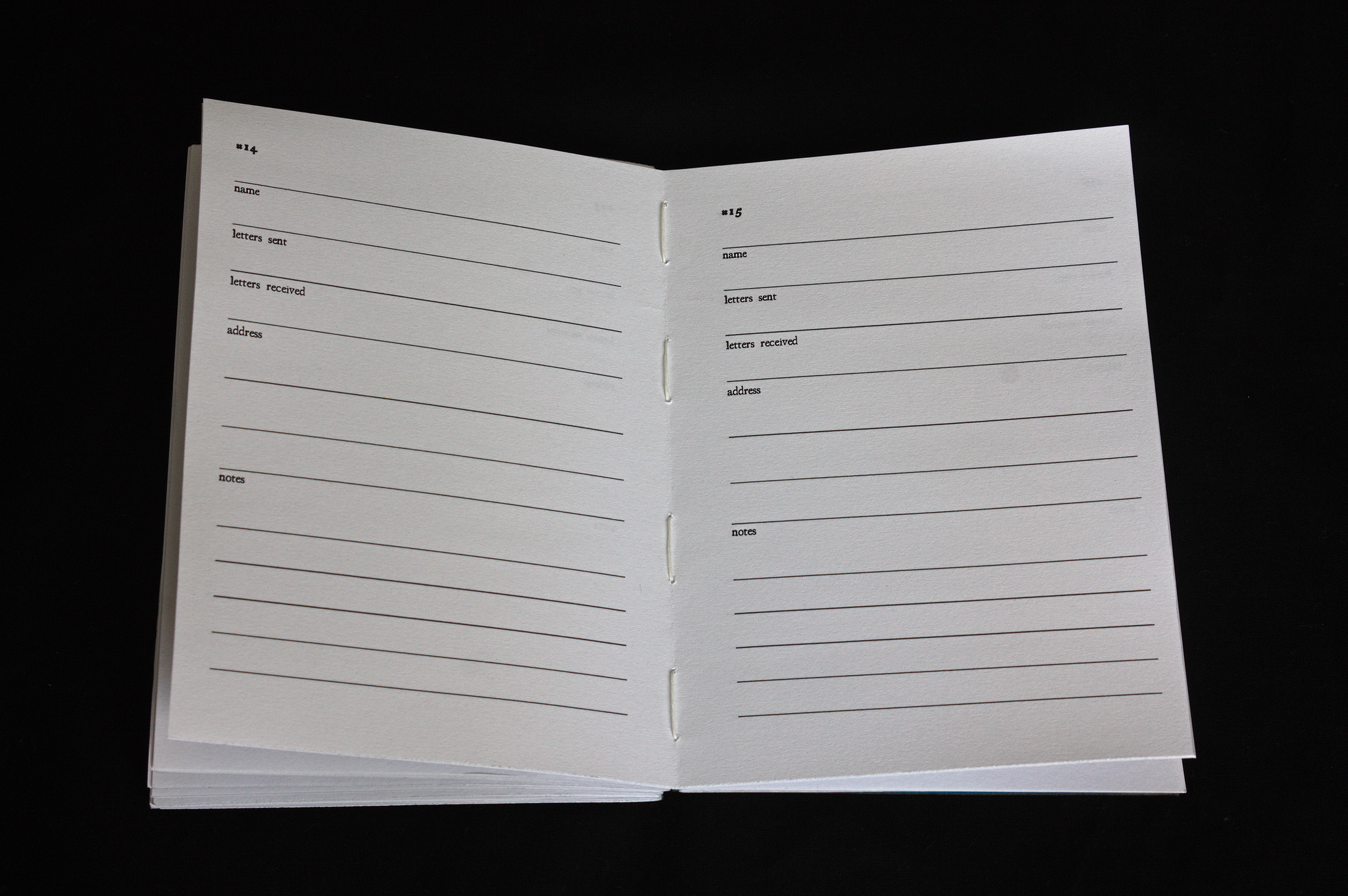 I ve also added a few pages for the addresses of my correspondents (and an index of the letters I ve exchanged with them), and a few empty pages for other notes.
Then I ve used my
I ve also added a few pages for the addresses of my correspondents (and an index of the letters I ve exchanged with them), and a few empty pages for other notes.
Then I ve used my 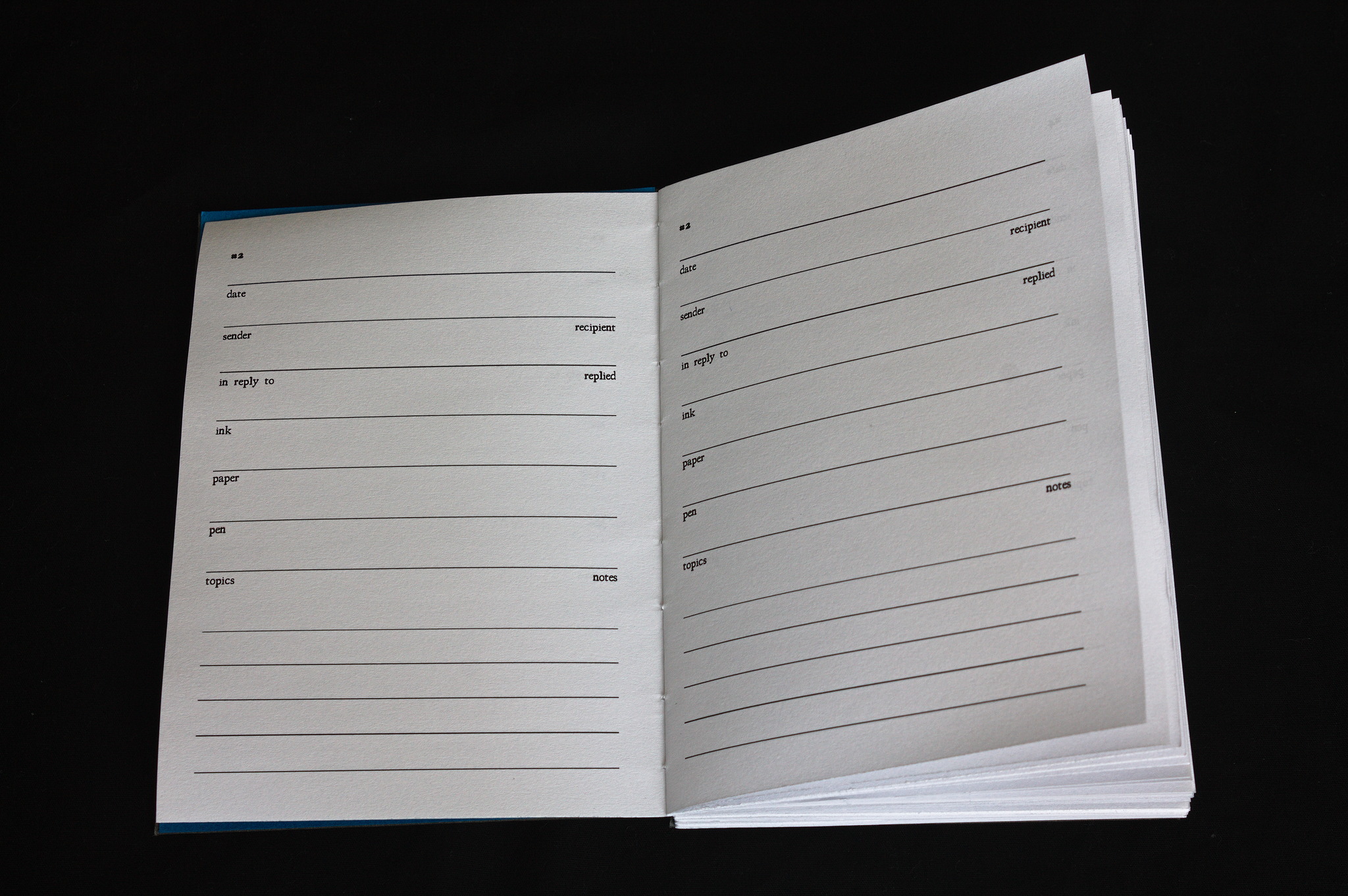 After printing (an older version where some of the pages are repeated. whoops, but it only happened 4 times, and it s not a big deal), it was time for binding this into a book.
I ve opted for Coptic stitch, so that the book will open completely flat and writing on it will be easier and the covers are 2 mm cardboard covered in linen-look bookbinding paper (sadly I no longer have a source for bookbinding cloth made from actual cloth).
After printing (an older version where some of the pages are repeated. whoops, but it only happened 4 times, and it s not a big deal), it was time for binding this into a book.
I ve opted for Coptic stitch, so that the book will open completely flat and writing on it will be easier and the covers are 2 mm cardboard covered in linen-look bookbinding paper (sadly I no longer have a source for bookbinding cloth made from actual cloth).
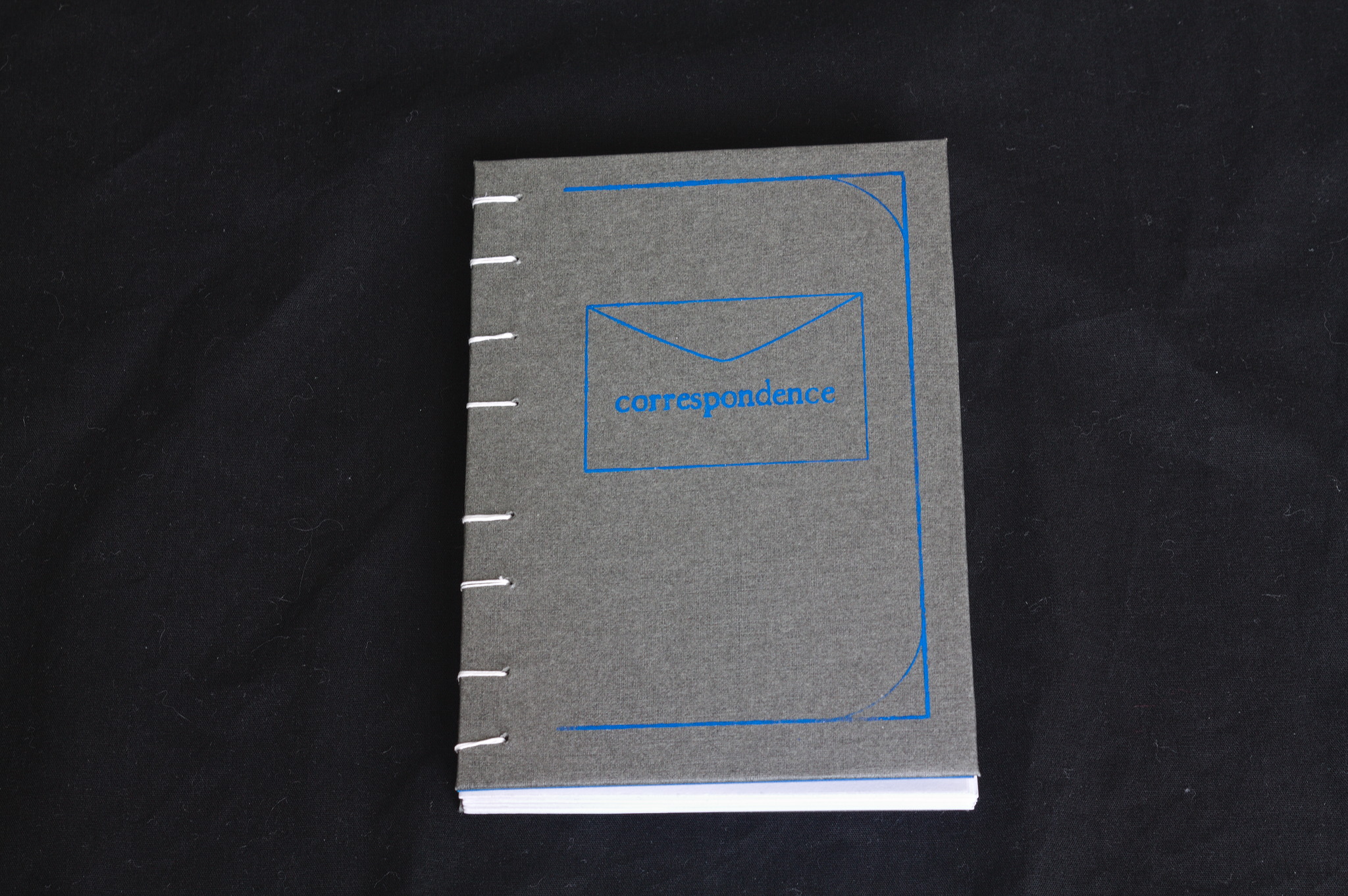 I tried to screenprint a simple design on the cover: the first attempt was unusable (the paper was smaller than the screen, so I couldn t keep it in the right place and moved as I was screenprinting); on the second attempt I used some masking tape to keep the paper in place, and they were a bit better, but I need more practice with the technique.
Finally, I decided that for such a Victorian thing I will use an Iron-gall ink, but it s Rohrer & Knlingner Scabiosa, with a purple undertone, because life s too short to use blue-black ink :D
And now, I m off to write an actual letter, rather than writing online about things that are related to letter writing.
I tried to screenprint a simple design on the cover: the first attempt was unusable (the paper was smaller than the screen, so I couldn t keep it in the right place and moved as I was screenprinting); on the second attempt I used some masking tape to keep the paper in place, and they were a bit better, but I need more practice with the technique.
Finally, I decided that for such a Victorian thing I will use an Iron-gall ink, but it s Rohrer & Knlingner Scabiosa, with a purple undertone, because life s too short to use blue-black ink :D
And now, I m off to write an actual letter, rather than writing online about things that are related to letter writing.








